Access Control Software Security
A well designed access control software should have extensive security features and should streamline system management. The more access points and users that a location has, the more important it is to have simplified, easy-to-use access control software.
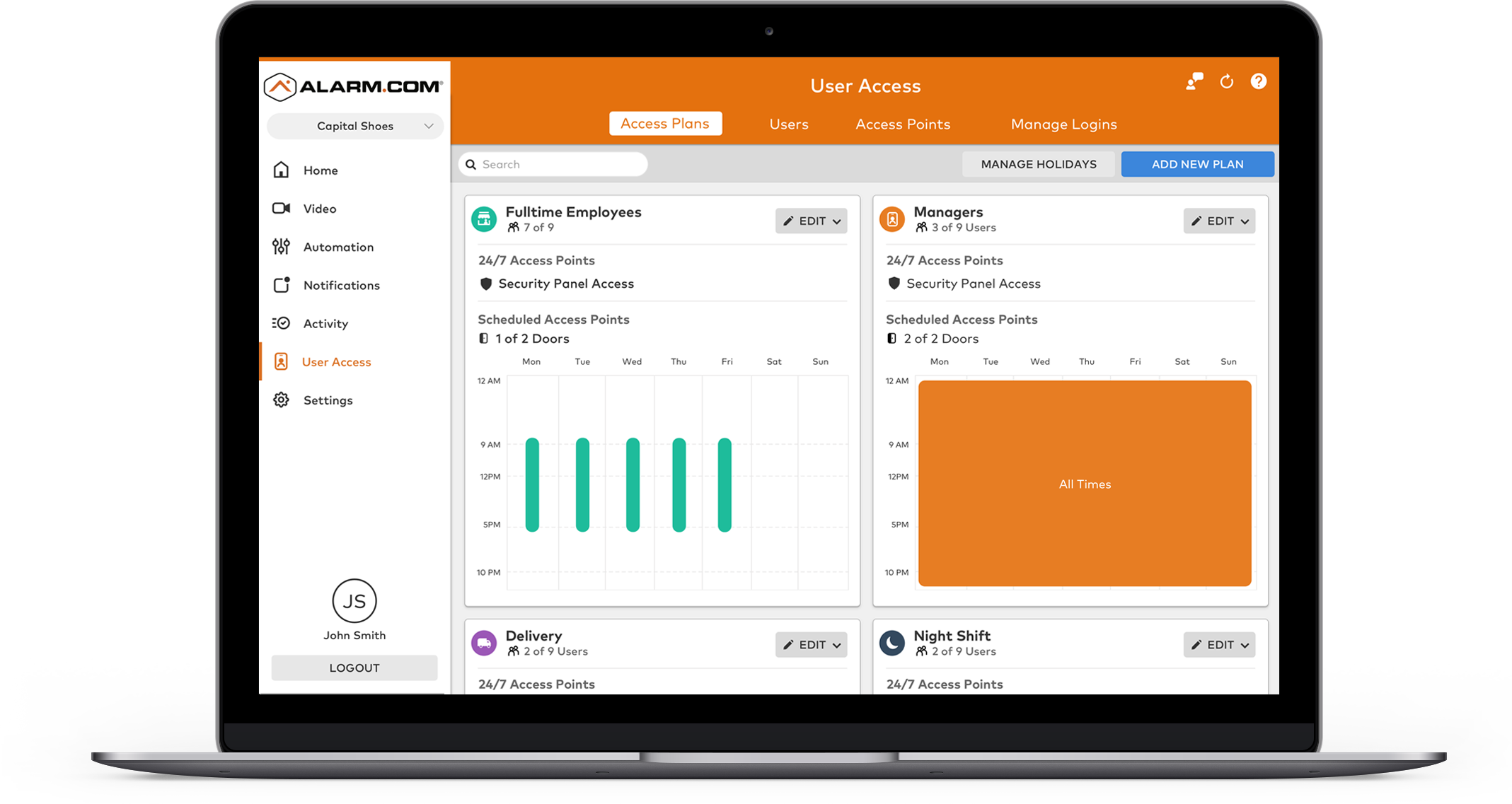
Access control systems should include tracking of activity and usage, reporting, a simple settings editor, and granular permissions that enable administrators to set custom permissions for specific users. With providers such as Brivo, Alarm.com, Avigilon, and more, True Protection has the customized access control solution you need for your business.
Next-Gen Business Control from True Protection
All-in-one security system, access control, and video surveillance systems offered by True Protection are designed to make enterprise management easier.
Your business, small or large, will benefit from a Smarter Access Control. Our latest technology offers adaptable security monitoring features appropriate for all types of businesses.
Business Access Control & Monitoring with Alarm.com
Manage your business security from the palm of your hands with True Protection and Smart Access Control on the alarm.com Platform.
True Protection understands the complexity of owning a business. Our Smart Access Control products allow you to worry less. Our versatile and adaptable security monitoring tools offer great benefits for business owners.
Why You Should Use a Cloud-Based Access Control System
Cloud-based systems are an effective and innovative way to manage and access the incredibly high amount of information in the system of a multi-site organization. Instead of spending the time and money to hire an in-house access administrator, use a cloud-based system that streamlines the access process securely.
The simplification of access with a cloud-based system includes remote access to add or remove permissions, remote door management, security through cloud-based encryption, and over-the-air data sending. The system also cuts in-person security costs and creates a central security process for all locations.